…to allow enterprises to make their key resources available to developers, mobile apps, consumers and other companies. They are one of the main ways that technology companies integrate with each… … Read More
Search Results for 5V0-92.22 Übungsfragen: VMware Carbon Black Cloud Audit and Remediation Skills - 5V0-92.22 Dateien Prüfungsunterlagen 🛷 Suchen Sie auf der Webseite “ www.itzert.com ” nach ➽ 5V0-92.22 🢪 und laden Sie es kostenlos herunter 🦇5V0-92.22 Fragen Und Antworten
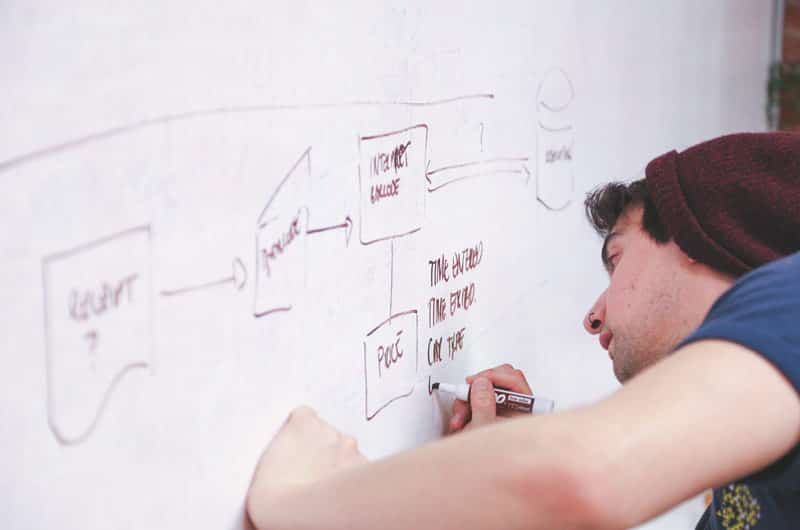
Usability Testing: Your Questions Answered
…ullamcorper vitae, dapibus a metus. Proin blandit consectetur sapien, sit amet pulvinar est commodo finibus. Donec neque metus, dictum vel lacus ac, aliquet varius neque. Vestibulum sed ex dui. Nulla facilisi…. … Read More

Authentication and Authorization: Reducing The Risk While Still Enabling Collaboration
…formats and transport protocols, including current and legacy messaging protocols to support non-HTTP services. Authorization capabilities include role-based, attribute-based, and content-based (payload): Multi-Factor Authentication Single Sign-On (SSO) Role Based, Attribute… … Read More

Protecting Against OAuth Hacks
…application back-end. Unfortunately, this is only one of many common developers–centric mistakes we see on a regular basis. For example, in some cases, OAuth identity providers return unsecured user data… … Read More

Protecting your API Listener through SSL
…returns -2.22 degrees Celsius. Log into the Forum Sentry web-based administrator and select Gateway –> WSDL Policies from the navigation panel. Enter the URL for the TempConvert service description shown… … Read More
API Security and MySQL — A match made in Hell
…tiny bit more secure? Not at all – due to added complexity it’s in fact even more open to malicious attacks. For complete article, see: The Cargo Cult of Cybersecurity.”… … Read More
WEBINAR: ABAC – The Convergence of API Security and Identity Management
Date: Thursday, March 19, 2015 | 2:00 p.m.-3:00 p.m. EST Presenter: Jason Macy, Chief Technology Officer, Forum Systems As agencies and organizations increase access to services and applications, the need… … Read More
CSO Review: Protecting API Connections with Forum Sentry
“The Forum Sentry API Security Gateway goes beyond access control and deep into security, monitoring all the connections that it forms between systems and enforcing very granular security policies.”… … Read More

How to Save Resources with Centralized API Security
…represented as (number of system^2)*8 but in a centralized model with a gateway, it is represented as (number of systems *2)*4. The gateway only requires one path per service/application but… … Read More
API Security Critical to Federal IT Modernization Strategy
…(SOAP/XML, REST/JSON, RPC, GWT, etc.). These APIs are often unprotected and contain numerous vulnerabilities,” according to the OWASP report.. OWASP has identified five key steps for protecting APIs. The organization… … Read More